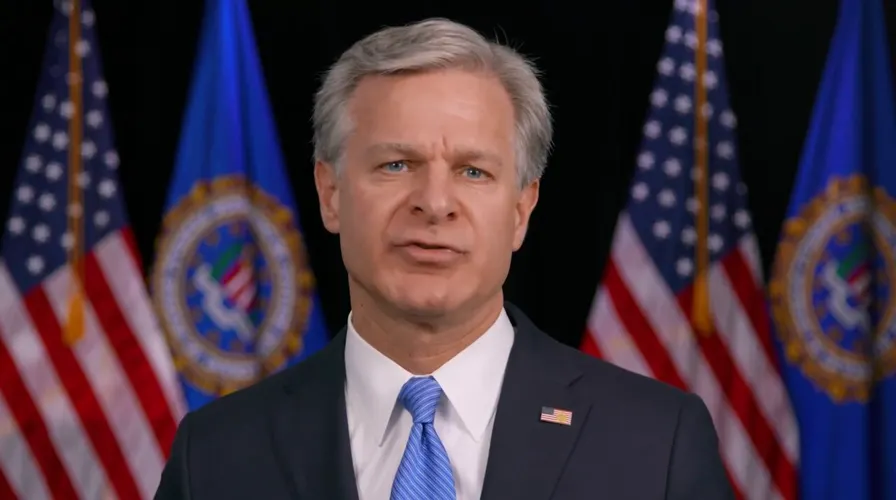
A recent report reveals a cyberattack attributed to Iran that targeted the Director of the FBI, raising new concerns about cybersecurity in the United States. The incident comes at a sensitive time as tensions between Iran and the U.S. escalate, highlighting the increasing threats faced by U.S. government institutions.
According to informed sources, the breach was executed using sophisticated methods, reflecting Iran's capability to carry out complex cyber espionage operations. This attack is part of a series of cyberattacks targeting critical infrastructure in the United States, raising questions about the readiness of the U.S. government to confront these threats.
Details of the Incident
Reports indicate that the breach targeted the information systems of the FBI Director, where hackers managed to access sensitive data related to ongoing investigations. This type of attack showcases Iran's ability to exploit security vulnerabilities in U.S. systems and heightens concerns about cybersecurity in the country.
This incident occurs amid escalating tensions between Iran and the United States, particularly following Washington's withdrawal from the nuclear agreement and the reimposition of sanctions on Tehran. These circumstances may have contributed to Iran's decision to carry out such operations as a means of pressuring the U.S. government.
Background & Context
Historically, Iran has been considered one of the leading nations in executing cyberattacks against Western countries. In recent years, the United States has experienced numerous cyberattacks attributed to Iran, including attacks on critical infrastructure and major corporations. These attacks demonstrate how cyberspace has become a new battleground for conflicts between nations.
Furthermore, Iran has developed its capabilities in the field of cyber warfare as part of its military strategy. This development underscores the significance of cyberspace as a tool for influence and pressure in international conflicts.
Impact & Consequences
This breach is expected to have a significant impact on relations between Iran and the United States. The incident may escalate tensions, as the U.S. will likely seek to take countermeasures to protect its infrastructure from cyber threats. It may also lead to increased spending on cybersecurity within government institutions.
Moreover, this breach could encourage other nations to develop their capabilities in cyberattacks, complicating the global security landscape. At the same time, it may enhance cooperation among countries to address these threats.
Regional Significance
The Arab region is considered part of this escalating cyber conflict, where countries may be directly affected by the repercussions of these attacks. Some nations may seek to bolster their cybersecurity capabilities to counter potential threats, especially amid ongoing political tensions.
This incident also highlights the importance of regional and international cooperation in addressing cyber threats, as cybersecurity has become a global issue requiring coordination among nations.
In conclusion, this breach serves as evidence of the increasing threats faced by the United States and the world, necessitating urgent action to enhance cybersecurity and protect sensitive information.